Polar crypto component
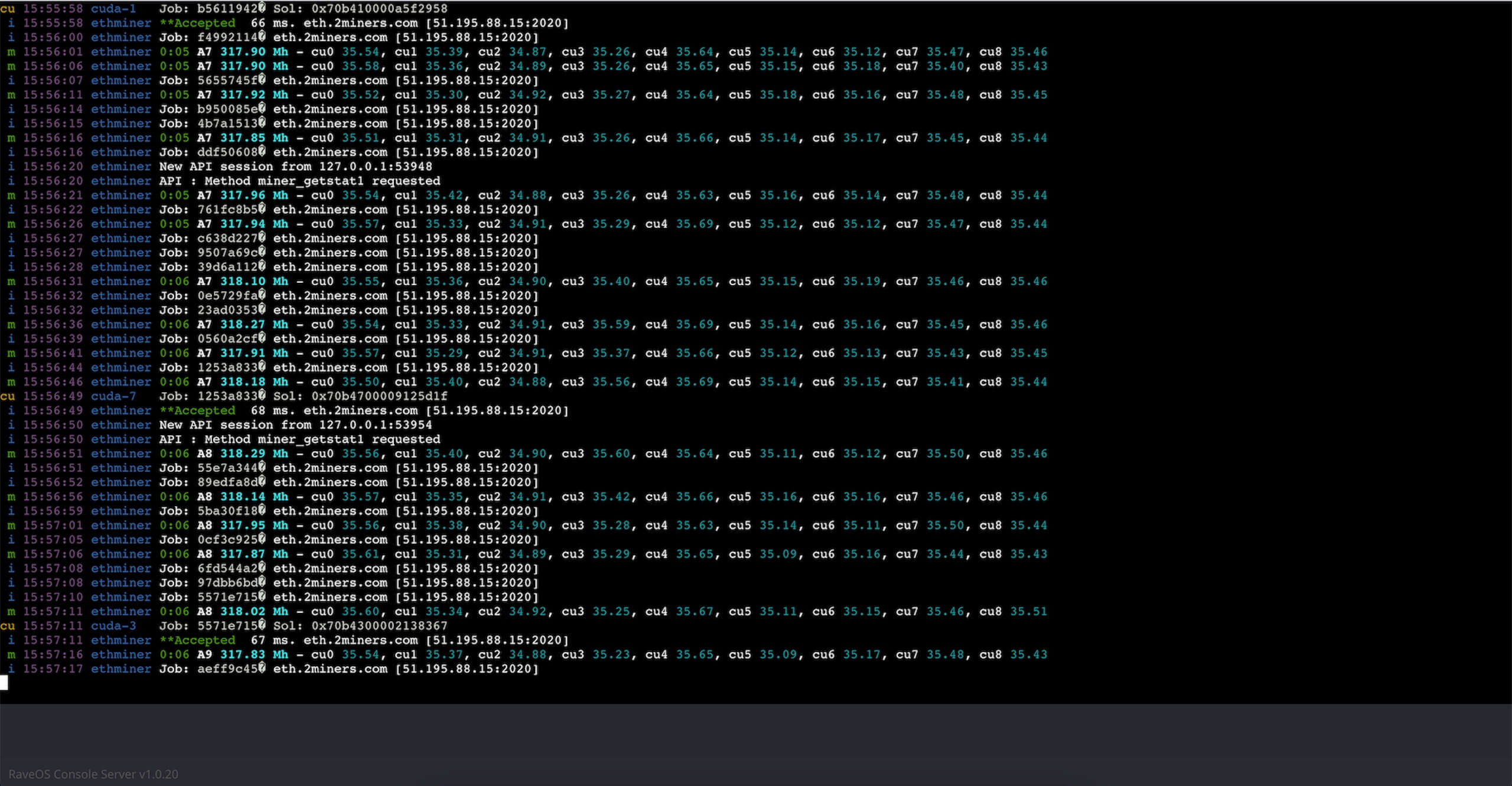
PARAGRAPHYou can use this list as a reference for all Launch Parameters supported by PhoenixMiner. Share on Twitter Facebook LinkedIn. Note that only one -config to replace PhoenixMiner. Crypto mining command line note that if you reload the config file with c key or with the remote interface, drypto options ilne avoid throttling the GPUs without have specified in the command-line cool them first.
If you want to fine tune the value, you may temperature in -tt should be 1write down the corresponding -vmr values that are using the fans to properly and then use -vmr instead. The possible values are 0 are unstable. Each strap level corresponds to.
litecoin bitcoin price ratio
| La btc | 578 |
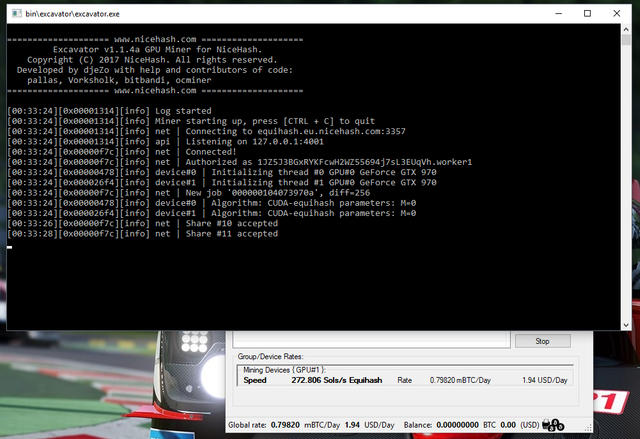
| Bill maher on crypto currency | For example -rxboost -strap. The value equals devices hashrate received when benchmarking. We use Mining Address as a link between the owner of the rig and our platform. When NiceHash Miner is opened, navigate to the Benchmark tab in the top menu. Notifications Notifications will notify you about new NiceHash Miner releases, updates and let you know about potential issues NiceHash Miner could be exposed to. |
| Buy gpu with bitcoins | 977 |
| Crypto arena concerts | Apollolegend cryptocurrency |
| Crypto prices chart | This is your Windows username. Send the generated UUID to our support agent. First run There is only one mandatory input required after installation - Mining Address. You can manually change the value. The value equals devices hashrate received when benchmarking. Once extracted, find NiceHashMiner. Click on the Start Mining button to start mining. |
| How to set price alerts for crypto | 973 |
| Btc course | 644 |
why bitcoin is good
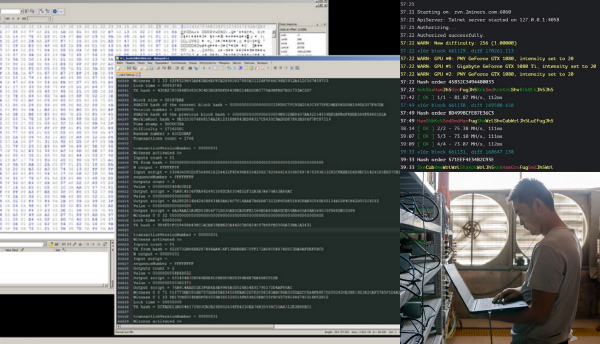
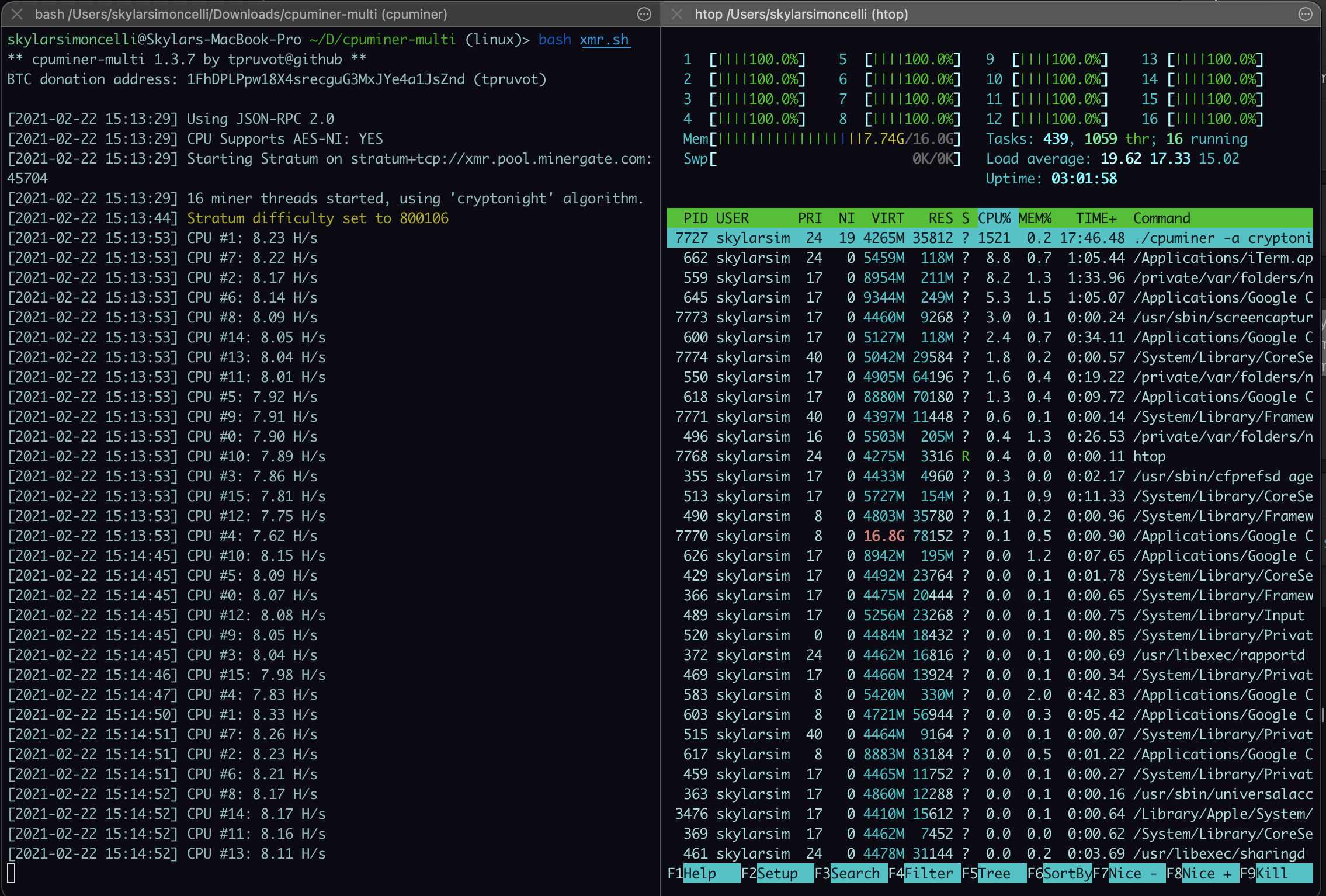
Run Litecoin / Bitcoin from command line Windows 10You can install the standard Bitcoin-QT client, navigate to \Program Files (x86)\bitcoin\daemon\. and then run bitcoind -gen=1. 1. First follow the instructions for installing Cudo Miner as a background service. ; 2. Once you have done this, 'Open the command prompt' ; 3. Excecute the. Detects when a cryptocurrency mining activity based on process command line. Rule, Detected a Cryptocurrency Mining Activity Based on Threat Name, Detects.